This phish provides plenty of tip-offs to its true nature, but someone glancing at it might be taken in. The “from” address is an actual Penn State address, but it belongs to an individual user whose account was compromised and used to send the messages – messages about your account won’t come from a person, they will come from the IT Service Desk or your department. The “to” address is a Penn State address that doesn’t actually exist, so it definitely isn’t the address of anyone who received it. The greeting on the message couldn’t be any more generic, and the poor grammar used here is a big clue that the message is bogus. The link, despite its lack of clarity, points to a forged WebAccess page which is similar to the real thing, but has a strange “submit” button and is clearly hosted on the Sitey service.
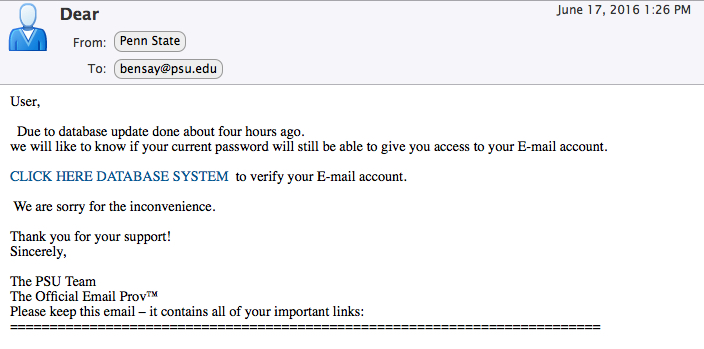
From: “Penn State” <xxxxxx@psu.edu>
To: bensay@psu.edu
Sent: Friday, June 17, 2016 1:26:29 PM
Subject: Dear
User,
Due to database update done about four hours ago.
we will like to know if your current password will still be able to give you access to your E-mail account.
CLICK HERE DATABASE SYSTEM (<- points to a forged WebAccess page on Sitey) to verify your E-mail account.
We are sorry for the inconvenience.
Thank you for your support!
Sincerely,
The PSU Team
The Official Email Prov™
Please keep this email – it contains all of your important links:
==========================================================================